CMS Security - WordPress
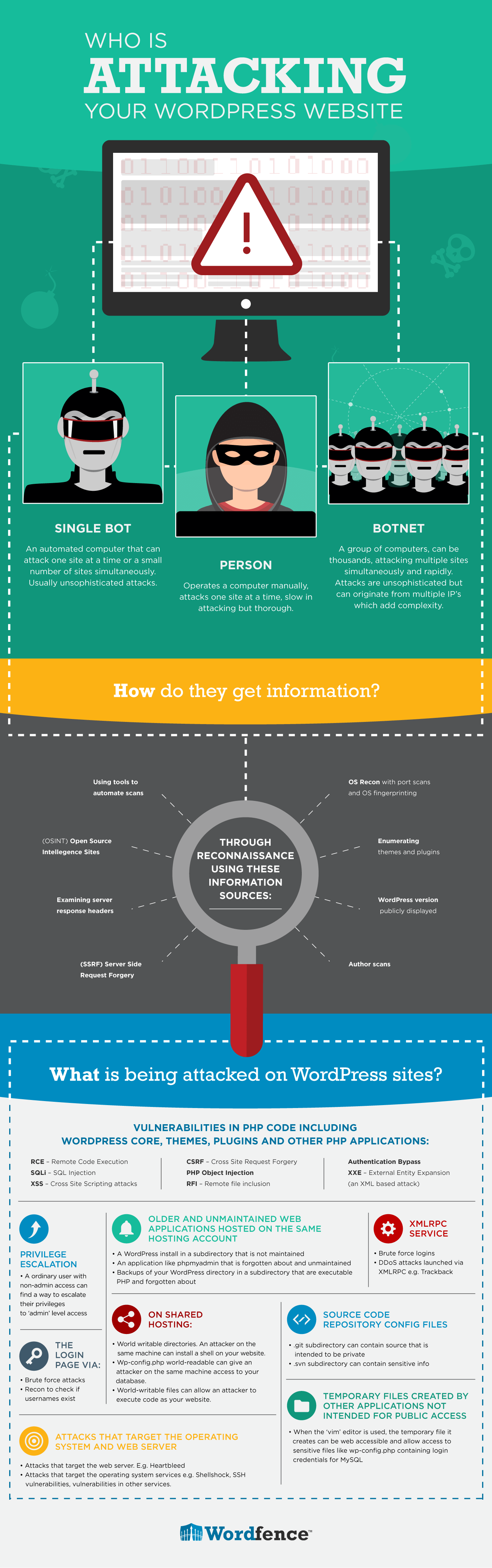
1. WordPress Vulnerabilities
- Common Vulnerabilities and Exposures (CVE) *
- WPScan Vulnerability Database *
- WordPress Security Category Archive *
- Dxwsecurity *
Consequences of using Outdated WordPress
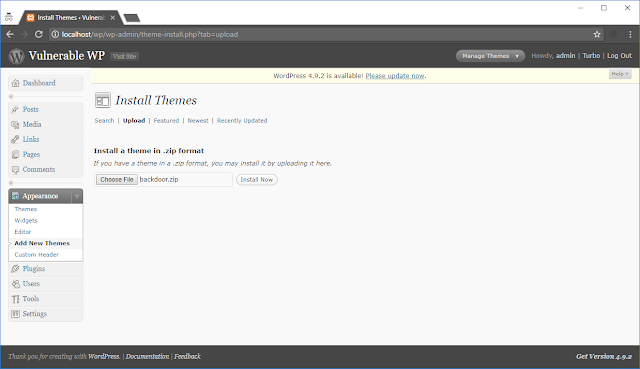 |
| Create a zip file which consist of a backdoor file |
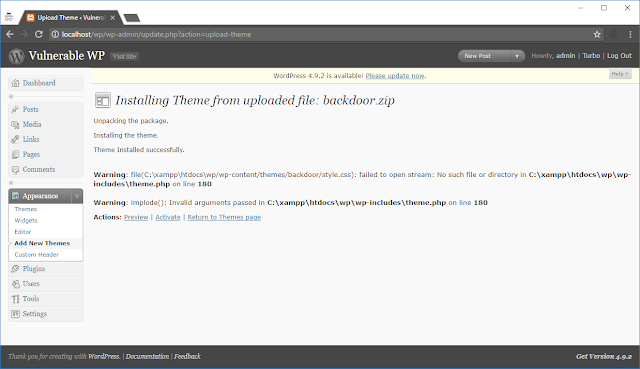 |
| WordPress shows "Theme installed successfully" |
 |
| Navigate to the path disclosed during the installation |
 |
| Pwned! |
2. WordPress Security Issues & Threats
2.1 WordPress Release Archive
https://wordpress.org/download/release-archive/2.2 WordPress Username Enumeration *
2.3 Disable User Registration If Not Needed
2.4 Delete readme.html and install.php
3. WordPress Hardening Recommendations
3.1 Data Backups
3.2 Access Control
3.2.1 2 Factor Authentication- Rublon Two-Factor Authentication
- Two-Factor
- Duo Two-Factor Authentication
- Authy Two Factor Authentication
3.2.2 Password
3.3 Core Directories/Files
3.3.1 File Permission
Directory: 775 (drwxr-xr-x)
Files: 644 (-rw-r--r--)
find /path/to/your/wordpress/install/ -type d -exec chmod 755 {} \;
find /path/to/your/wordpress/install/ -type f -exec chmod 644 {} \;
Avoid having any file or directory set to 777!
3.3.2 WP-* *
Restrict Access to wp-admin Directory
- Create passwords for .htpasswd files using Htpasswd Generator
- Copy the text generated into .htpasswd file
- Create a .htaccess file in /wp-admin/ directory with the following codes
Prevents normal site visitors from accessing /wp-admin/admin-ajax.php
Add the following codes in .htaccess file.
<Files admin-ajax.php>
Order allow,deny
Allow from all
Satisfy any
</Files>
Prevents normal site visitors from accessing WP-Includes
Add the following codes in .htaccess file.
# Block the include-only files.
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ - [F,L]
RewriteRule !^wp-includes/ - [S=3]
RewriteRule ^wp-includes/[^/]+\.php$ - [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+\.php - [F,L]
RewriteRule ^wp-includes/theme-compat/ - [F,L]
</IfModule>
# BEGIN WordPress
Note:
Place it outside the # BEGIN WordPress and # END WordPress tags in the .htaccess file.
WordPress can overwrite anything between these tags.
WP-Content/Uploads
Add the following codes in .htaccess file.
# Kill PHP Execution
<Files ~ "\.ph(?:p[345]?|t|tml)$">
deny from all
</Files>
WP-Config.php
Add the following codes in .htaccess file.
<files wp-config.php>
order allow,deny
deny from all
</files>
Disable File Editing
Append the following two lines to the end of your wp-config.php file
## Disable Editing in Dashboard
define('DISALLOW_FILE_EDIT', true);
3.4 Security Plugins
- Sucuri Security – Auditing, Malware Scanner and Security Hardening *
- Wordfence Security *
- iThemes Security *
- Loginizer *
- NinjaFirewall (WP Edition) *
4. WordPress Security Guideline
- OWASP Wordpress Security Implementation Guideline *
- Hardening WordPress *
- Wordpress Security Functions for paranoid folks *
5. Checklist – How to Secure Your WordPress Website

Download the PDF here:
6. Testing WordPress Security and Misconfiguration
6.1 WPScan - black box WordPress vulnerability scanner *
Run all enumeration tools
root@kali:~# wpscan --url http:// --enumerate
6.2 Nikto *
root@kali:~# nikto -h <target_url>
References:
Hardening WordPress *
The WordPress Security Learning Center *
Top tips to prevent a WordPress hack *
WordPress Security News:
201806
E-Commerce Websites Exposed To Hackers Due To Vulnerable WordPress PluginsPopular posts from this blog
Remote Desktop Protocol (RDP) Security
Common Remote Desktop Protocol (RDP) Vulnerabilities Terminal Services Encryption Level is Medium or Low Microsoft Windows Remote Desktop Protocol Server Man-in-the-Middle Weakness Terminal Services Doesn't Use Network Level Authentication (NLA) Only Terminal Services Encryption Level is Medium or Low Vulnerability Assessment: Host Assessment: Remediation: Local Computer Policy/Computer Configuration/Administrative Templates/Windows Components/Remote Desktop Services/Remote Desktop Session Host/Security/Set client connection encryption level Set client connection encryption level to High Note: High: The High setting encrypts data sent from the client to the server and from the server to the client by using strong 128-bit encryption. Use this encryption level in environments that contain only 128-bit clients (for example, clients that run Remote Desktop Connection). Clients that do not support this encryption level cannot connect to RD S...
Penetration Testing - Network
Manual Vulnerability Assessment TCP/21: FTP Anonymous FTP Enabled anonymous guest TCP/22: SSH nmap -p 22 --script ssh2-enum-algos <ip_address> SSH Weak Algorithms Supported SSH Server CBC Mode Ciphers Enabled ssh -oCiphers=<ciphers> <ip_address> SSH Weak MAC Algorithms Enabled ssh -oMACs=<algorithm> <ip_address> SSH Protocol v1 Supported ssh -1 <ip_address> -v Hardening on SSH Ciphers aes256-ctr,aes192-ctr,aes128-ctr MACs hmac-sha2-512-etm@openssh.com,hmac-sha2-256-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-512,hmac-sha2-256,umac-128@openssh.com TCP/23: Telnet Unencrypted Telnet Server telnet <ip_address> 23 TCP/25: SMTP SMTP Service Cleartext Login Permitted telnet <ip_address> 25 EHLO <ip_address> AUTH LOGIN Mailserver answer to VRFY and EXPN requests * nc <ip_address> 25 EXPN root VRFY root TCP/53: DNS DNS Server Cache Snooping Remote Information Disclosure ...
Damn Vulnerable Web Services (DVWS) - Walkthrough
Installation Damn Vulnerable Web Services (DVWS) is an insecure web application with multiple vulnerable web service components that can be used to learn real world web service vulnerabilities. https://github.com/snoopysecurity/dvws WSDL Enumeration Spider DVWS using Burp Suite and look for service.php Requests processed by SOAP service include check_user_information , owasp_apitop10 , population and return_price XPATH Injection User Login: 1' or '1'='1 User Password: 1' or '1'='1 Command Injection Original Request parameter value of name is " find " by default Edited Request change the parameter value of name from "find" to " dir " Cross Site Tracing (XST) Hint of " The NuSOAP Library service is vulnerable to a Cross-site scripting flaw " is given by DVWS. Exploit is published at exploit DB ( https://www.exploit-db.com/e...
Server Message Block (SMB) Security
Common SMB related vulnerabilities Microsoft Windows SMBv1 Multiple Vulnerabilities SMB Signing Disabled Microsoft Windows SMB NULL Session Authentication Microsoft Windows SMB Shares Unprivileged Access Network Discovery: TCP port 5357 - Web Services on Devices API (WSDAPI) File and Printer Sharing: TCP port 135 - Remote Procedure Call (RPC) TCP port 139 - NETBIOS Session Service TCP port 445 - Server Message Block (SMB) By disable NetBIOS over TCP/IP (TCP Port 139), NETBIOS name discovery will be prevented Microsoft Windows SMBv1 Multiple Vulnerabilities Vulnerability Assessment: NSE script smb-protocols can be used to check if the server supported NT LM 0.12 (SMBv1) . Host Assessment: Get-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters | ForEach-Object {Get-ItemProperty $_.pspath} Remediation: Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters...
Host Configuration Assessment - Windows
OS Information Gathering systeminfo wmic computersystem get domainrole 0 - Standalone workstation 1 - Member workstation 2 - Standalone server 3 - Member server 4 - Domain controller secedit /export /cfg cfg.ini > nul net user administrator > netuseradmin.txt auditpol.exe /get /category:* > auditpol.txt netsh advfirewall show allprofiles > firewall.txt net accounts > netaccount.txt gpresult /f /h evid/gporesult.html > nul accesschk /accepteula -q -a * > accesschk.txt *Simplify the process with Scgary ! User Right Assignment type cfg.ini | grep "^SeAuditPrivilege\|^SeCreatePagefilePrivilege\|^SeRemoteShutdownPrivilege\|^SeRemoteInteractiveLogonRight\|^SeEnableDelegationPrivilege\|^SeLockMemoryPrivilege\|^SeDenyNetworkLogonRight\|^SeChangeNotifyPrivilege\|^SeDebugPrivilege\|^SeDenyBatchLogonRight\|^SeCreateGlobalPrivilege\|^SeShutdownPrivilege\|^SeIncreaseQuotaPrivilege\|^SeTrustedCredManAccessPrivilege\|^SeDenyIn...
Offensive Security Testing Guide
This cheat sheet compiles the commands we learned to exploit vulnerable machines. However, these commands alone may not be sufficient to obtain your Offensive Security Certified Professional (OSCP) certification. So... Try Harder! Information Gathering Operating System Windows Interesting Path "Documents and Settings"/Administrator/Desktop file:///C:/xampp/readme_en.txt file:///C:/xampp/passwords.txt file:///C:/xampp/webdav/webdav.txt file:///C:/xampp/apache/conf/extra/httpd-dav.conf file:///C:/xampp/apache/conf/extra/httpd-xampp.conf file:///C:/xampp/apache/logs/access.log file:///C:/xampp/apache/logs/error.log file:///C:/xampp/security/webdav.htpasswd file:///C:/xampp/htdocs/dashboard/phpinfo.php file:///C:/xampp/phpmyadmin/config.inc.php file:///C:/xampp/php/logs/php_error_log file:///C:/xampp/mysql/bin/my.ini C:\Users\<User>\AppData\Local\Temp #Email Address C:\Users\<User>\AppData\Local\Microsoft\Outlook Active Connection netstat -...
Web Server Hardening - Apache Tomcat
Reference: https://tomcat.apache.org/tomcat-8.0-doc/security-howto.html 1. Remove Extraneous Resources Removing sample resources C:\xampp\Tomcat\webapps\docs C:\xampp\Tomcat\webapps\examples Removing Manager Application if not using C:\xampp2\Tomcat\webapps\host-manager C:\xampp2\Tomcat\webapps\manager C:\xampp2\Tomcat\conf\Catalina\localhost\manager.xml Disable unused Connector C:\xampp2\tomcat\conf\server.xml cat server.xml | grep "Connector" 2. Limit Server Platform Information Leaks Alter the Advertised server information Audit: cd $CATALINA_HOME/lib jar xf catalina.jar org/apache/catalina/util/ServerInfo.properties grep server.info org/apache/catalina/util/ServerInfo.properties Remediation: server.info=<SomeWebServer> server.number=<someversion> server.built= Disable X-Powered-By HTTP Header and Rename the Server Value for all Connectors Turn off TRACE Affected file: $CATALINA_HOME/conf/server.xml Remediation:...
Content Page
The Cheat Sheets offer a variety of information security cheat sheets on various security assessments and provides code to simplify testing and verification processes. Penetration Testing Network CMS - WordPress Mobile - Android Mobile - iOS Web Service (API) Security Damn Vulnerable Web Services - Walkthrough OWASP Series 2017 A1 Injection 2017 A3 Sensitive Data Exposure 2017 A4 XML External Entities (XXE) 2017 A6 Security Misconfiguration 2017 A7 Cross-Site Scripting (XSS) 2017 A8 Insecure Deserialization Configuration Assessment Windows Linux Network Device Web Server Hardening Apache PHP MySQL SSL Security Database Assessment Oracle PostgreSQL Database Assessment Tool Host Device Hardening Server Message Block (SMB) Security Remote Desktop Protocol (RDP) Security Social Engineering Social Engineering Testing - Phishing Email Security Malware Exploitation using Shell Post Exploitation Physical ...
Mobile Penetration Testing - Android
Testing Environment Android Emulator Geny Motion: https://www.genymotion.com/fun-zone/ Android Debug Bridge (ADB) C:\Users\<User>\AppData\Local\Android\Sdk\platform-tools adb -s <specific device> shell #Specific Device adb -d shell #Device adb -e shell #Emulator Basic ADB command adb install <apk file> adb pull <location> adb push <file> <location> Basic Linux command cat /proc/version #Kernel version cat /proc/cpuinfo #Processor Information ps #Processes cat /system/etc/permissions/platform.xml #Permission and GID Information Gathering Retrieve APK file from Device (Recommended) adb shell pm list packages pm path <package> adb pull <apk path> Retrieve APK file from Internet https://apkpure.com To check the certificate information keytool -printcert -file CERT.RSA #C:\Program Files\Java\jre1.8.0_131\bin\keytool.exe Android Manifest Analysis 1. Activity, Service, Content Provider, Broadcast ...
Penetration Testing with OWASP Top 10 - 2017 A7 Cross-Site Scripting (XSS)
XSS flaws occur whenever an application includes untrusted data in a new web page without proper validation or escaping, or updates an existing web page with user-supplied data using a browser API that can create HTML or JavaScript. XSS allows attackers to execute scripts in the victim's browser which can hijack user sessions, deface web sites, or redirect the user to malicious sites. DOM-Based XSS Proof of Concept <html> <head> <title>DOM-based Cross-site Scripting</title> </head> <body> Hi, <script> var pos = document.URL.indexOf("name=")+5; //finds the position of value var userInput = document.URL.substring(pos,document.URL.length); //copy the value into userInput variable document.write(unescape(userInput)); //writes content to the webpage </script> </body> </html> XSS Validation Bypass <Script>alert(1)</script> <script<script>>alert(1)</script> <svg onload=...



















